To a large degree, building security is driven by the integration of a variety of electronic security systems. The market and engineering of these systems exploded in the post-9/11 era and has shown few signs of tapering off. “Rapid advances in technology and government directives are driving purchase decisions, especially in the replacement of legacy systems,” says the Security Industry Association in a recent report.
One challenge has been that security technology began to outpace the knowledge of many Building Teams. Their most daunting question: whether to adopt the latest and best technology, or to invest in a reasonably reliable, less expensive system that has a positive track record. The response by leading design and construction experts has been to plan ahead and work with system integrators for the facility being developed.
For large commercial and multifamily projects, Building Teams typically focus on three types of systems: 1) access control, 2) intrusion detection, and 3) visual surveillance.
Access control. Two electronic access technologies are at the forefront: biometrics and radio frequency identification (RFID). Of the two, RFID is the more commonplace: even less secure facilities may invest in simple ID tags with stored electronic information, such as public parking garages. RFID systems are widely available, and the tags and cards are essentially disposable.
The downside of most RFID technology is the ease of access to the stored information on the card. Smart cards, by contrast, constructed with an embedded chip, can be made highly secure and difficult to forge, duplicate, or hack, which allows for the safe storage of personal and sensitive information on the card. Though the smart card can be operated by proximity reading like an RFID tag to allow secure access to stored data or physical access to a secure area, smart card systems are more expensive than their chipless counterparts.
A recent trend in the industry is to consider the use of biometrics––identification through the scan of the occupant’s fingerprint, retina, or similarly unique biophysical aspect––in tandem with RFID, rather than as an alternative.
Two types of hybrid systems are currently in use: one with biometric and RFID systems independent of one another (essentially a redundancy system), and others that integrate the RFID and biometric systems natively. One of the first such systems employed a processor chip that required a positive fingerprint ID before releasing access to the information stored in the RFID tag.
Whether integrated or not, combining RFID and biometrics is currently seen as offering the highest levels of security.
Intrusion detection. According to the Security Industry Association report, 75% of those interviewed reported that their facilities were equipped with intrusion- and fire-detection systems. Of those without such systems, about 66% reported that they would need such a system within five years, and about half said they would have one installed within five years.
Apart from the fact that a majority of facilities use or will use electronic intrusion-detection and alarm systems, the market is otherwise divided on the types of systems to employ, and whether to integrate detection with other electronic systems.
Because there is always the possibility of false alarms, planning should include consideration of integrating intrusion detection with video surveillance or some other system for verification. This is especially important if the detection system is wired to alert police (or fire) response directly. According to the same SIA report, “Many communities are adopting ‘no-response’ policies to false alarms if they are not verified by audio, video, or eyewitnesses.”
Video surveillance. The technology behind a system of security cameras is an important decision that receives plenty of discussion during project planning. Closed-circuit television (CCTV) analog cameras recording onto a DVR may seem adequate until cost-benefit questions and systems integration issues arise. Analog signals can be encoded to digital, but the analog camera’s resolution will limit the recording’s quality, according to Sean A. Ahrens, Global Leader for Aon Fire Protection Engineering’s security consulting practice, who sits on standards-setting panels for both SIA and UL. Enhancement of an encoded digital image is much more difficult than that of direct digital.
Digital cameras are also preferred today because they are relatively inexpensive, even with high megapixel capture. The downside is the growing need for data storage, but that can be mitigated through programming to record only when the system detects a change from a reference frame. Especially useful in low-traffic environments, this aspect of direct digital technology offers flexibility for data storage requirements.
What’s more, this aspect dovetails with security integration schemes. The intrusion detection system that requires video verification to alert authorities can depend upon the digital camera to register any change in its recording field. High-megapixel cameras can also be integrated as a biometric access control, using facial recognition software.
Ahrens also points out that data storage concerns associated with direct digital are being addressed within the IT industry, through programs to encode and decode digital signals, called codecs. A new codec called H.264 requires substantially less data storage, about half that of MPEG-2, while enhancing video performance compared to what is currently available, or MPEG-4, says Ahrens. “Anyone considering the procurement of a digital recording solution should ensure that it is capable of running H.264 and other future and more robust codecs,” he says.
His advice: Be proactive now, and you will be able to garner future benefits. +
Related Stories
Fire-Rated Products | Apr 16, 2024
SAFTI FIRST launches redesigned website
SAFTI FIRST, leading USA-manufacturer of advanced fire rated glass and framing systems, is pleased to announce the launch of its newly redesigned website, safeglassforschools.com.
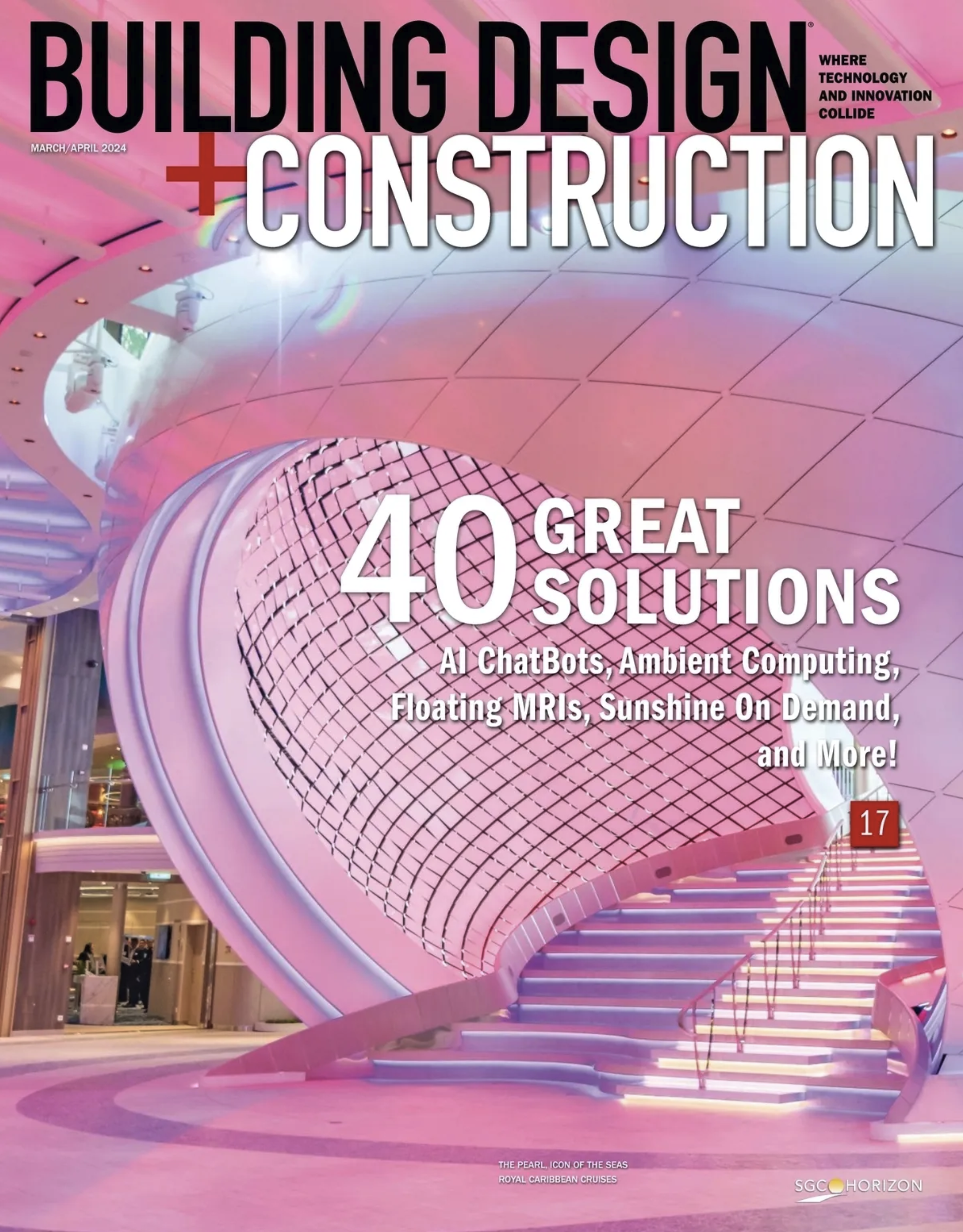
75 Top Building Products | Dec 13, 2023
75 top building products for 2023
From a bladeless rooftop wind energy system, to a troffer light fixture with built-in continuous visible light disinfection, innovation is plentiful in Building Design+Construction's annual 75 Top Products report.
Products and Materials | Aug 31, 2023
Top building products for August 2023
BD+C Editors break down 15 of the top building products this month, from frameless windscreens to smart fixture mount sensors.
Fire-Rated Products | Aug 14, 2023
Free download: Fire-rated glazing 101 technical guide from the National Glass Association
The National Glass Association (NGA) is pleased to announce the publication of a new technical resource, Fire-Rated Glazing 101. This five-page document addresses how to incorporate fire-rated glazing systems in a manner that not only provides protection to building occupants from fire, but also considers other design goals, such as daylight, privacy and security.
Sponsored | Fire and Life Safety | Jul 12, 2023
Fire safety considerations for cantilevered buildings [AIA course]
Bold cantilevered designs are prevalent today, as developers and architects strive to maximize space, views, and natural light in buildings. Cantilevered structures, however, present a host of challenges for building teams, according to José R. Rivera, PE, Associate Principal and Director of Plumbing and Fire Protection with Lilker.
Fire and Life Safety | Jan 9, 2023
Why lithium-ion batteries pose fire safety concerns for buildings
Lithium-ion batteries have become the dominant technology in phones, laptops, scooters, electric bikes, electric vehicles, and large-scale battery energy storage facilities. Here’s what you need to know about the fire safety concerns they pose for building owners and occupants.
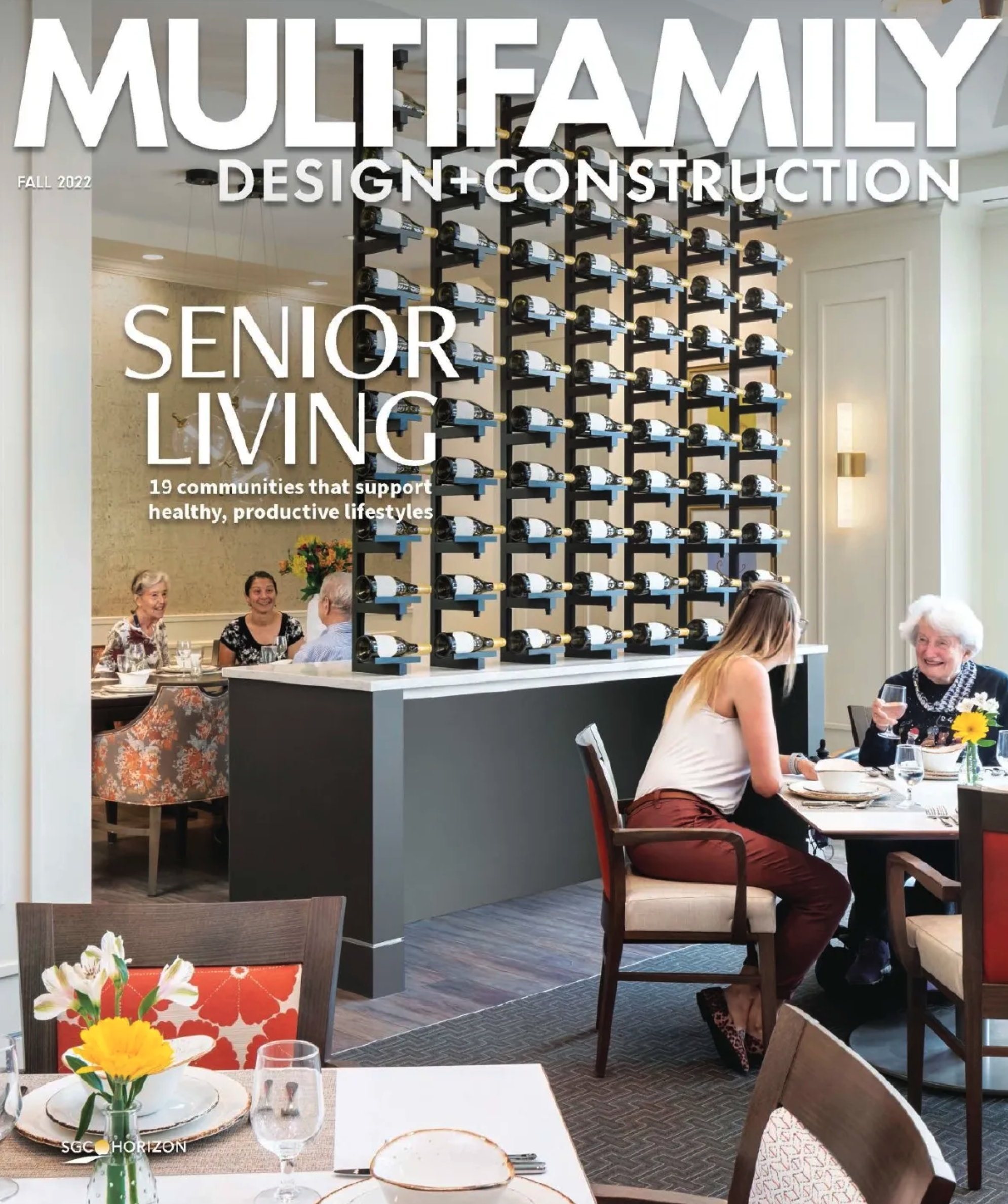
Codes and Standards | Dec 29, 2022
New York City multifamily owners concerned over fires caused by e-bikes
In 2022, there have been nearly 200 fires and six deaths in New York City caused by lithium-ion batteries used in mobility devices such as electric bikes and scooters.
Sponsored | Resiliency | Dec 14, 2022
Flood protection: What building owners need to know to protect their properties
This course from Walter P Moore examines numerous flood protection approaches and building owner needs before delving into the flood protection process. Determining the flood resilience of a property can provide a good understanding of risk associated costs.
Resiliency | Nov 8, 2022
Oregon wildfire risk law prompts extensive backlash from property owners
A bipartisan bill aimed at protecting property owners from wildfires that was passed by the Oregon legislature has prompted a strong backlash.
Fire and Life Safety | Oct 4, 2022
Fire safety considerations for cantilevered buildings
Bold cantilevered designs are prevalent today, as developers and architects strive to maximize space, views, and natural light in buildings. Cantilevered structures, however, present a host of challenges for building teams, according to José R. Rivera, PE, Associate Principal and Director of Plumbing and Fire Protection with Lilker.